
Exactly what you are missing
Simple and modular Analytics and Access Governance Services
Companies often complain about their current Identity Management solution: Missing functionalities, costly customization, shallow analytics, and low usability and missing user experience.
With NEXIS 4 you found your perfect Access Governance companion. We offer world-class analytics and end-user experience without the need of expensive integration and coding work. Do not waste your time with unnecessary and expensive manual work. NEXIS 4 seamlessly extends your existing IAM-tooling with easily configurable and modular self-services – exactly what you are missing.
We are convinced that algorithms alone are not the solution for Access Governance success. You are only going to reach your goal if your IT and business departments collaborate to tackle modern Identity Management challenges. NEXIS 4 provides numerous configurable UI components and functions for a whole new user experience. It motivates your business users to join your Access Governance mission.

The perfect solution
for your IT and business
The Swiss Army knife for your IT
IT departments love NEXIS 4 for its intelligent analytics and the perfect visualizations, optimizations, and controls of your digital identities, roles, and entitlements.
Tailor-made for business users
Non-IT stakeholders love NEXIS 4 for its configurable, intuitive user interfaces and our custom self-services that finally let Access Governance speak the business language.
NEXIS 4
Functions
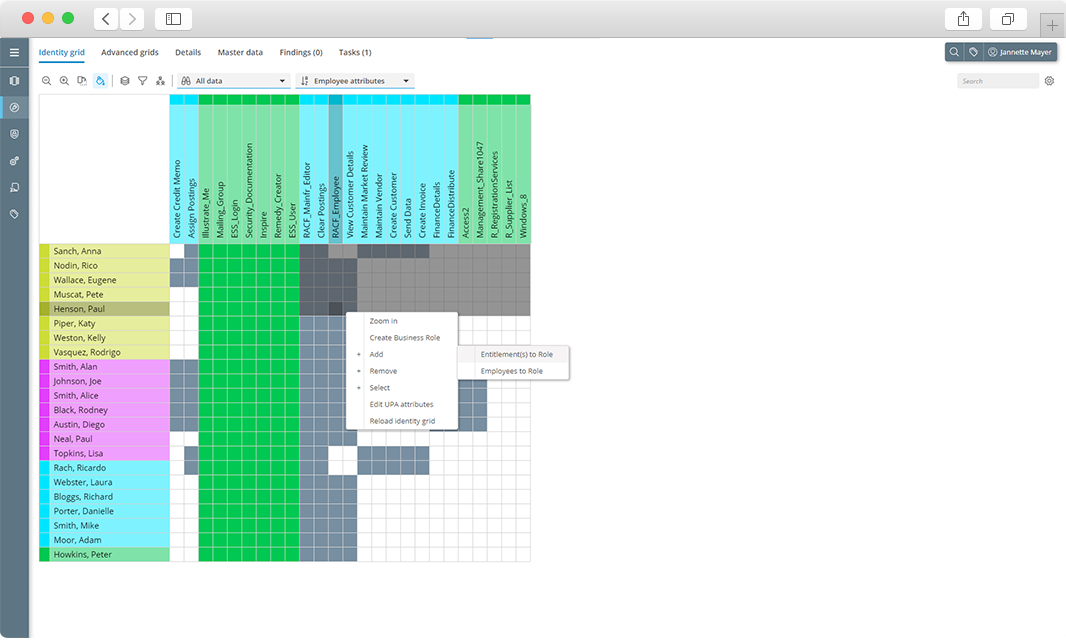
Analytics & visualization
360° Identity and Role Analytics scan your entitlements and simulate the best future business role structures for you. From configurable tables to more than 20 grid-based matrices, we’ve built a rich set of views to help you visualize every angle of your data.
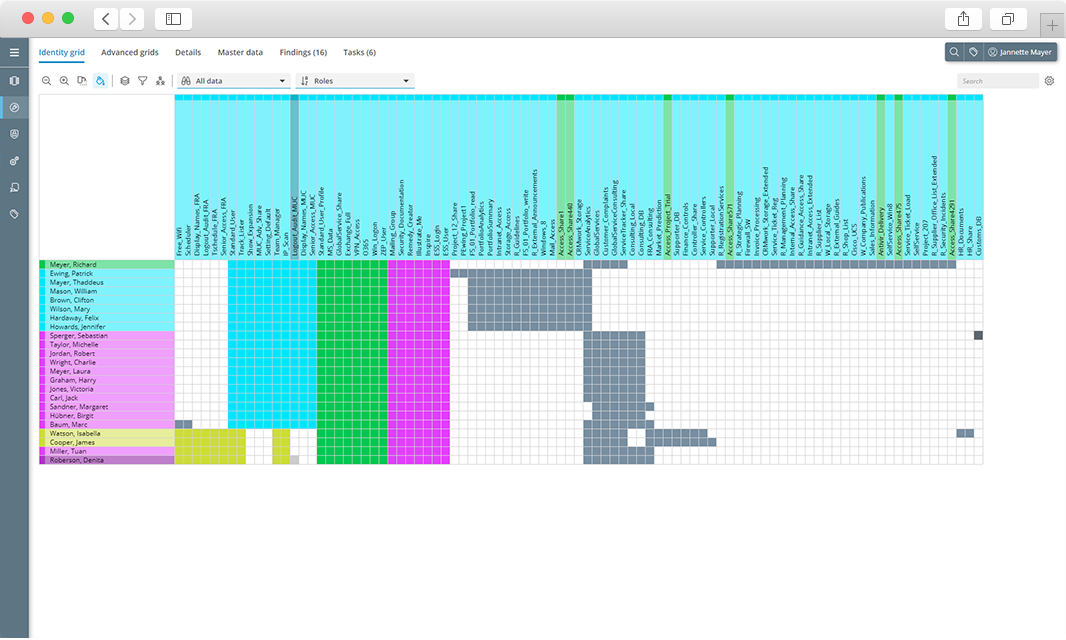
Role modeling & optimization
With our powerful algorithms and intuitive visualizations, the design of rule-based or static business roles becomes as simple as possible. NEXIS 4 also supports you during company re-structuring or onboarding of new applications with automatically generated recommendations for authorization re-design.
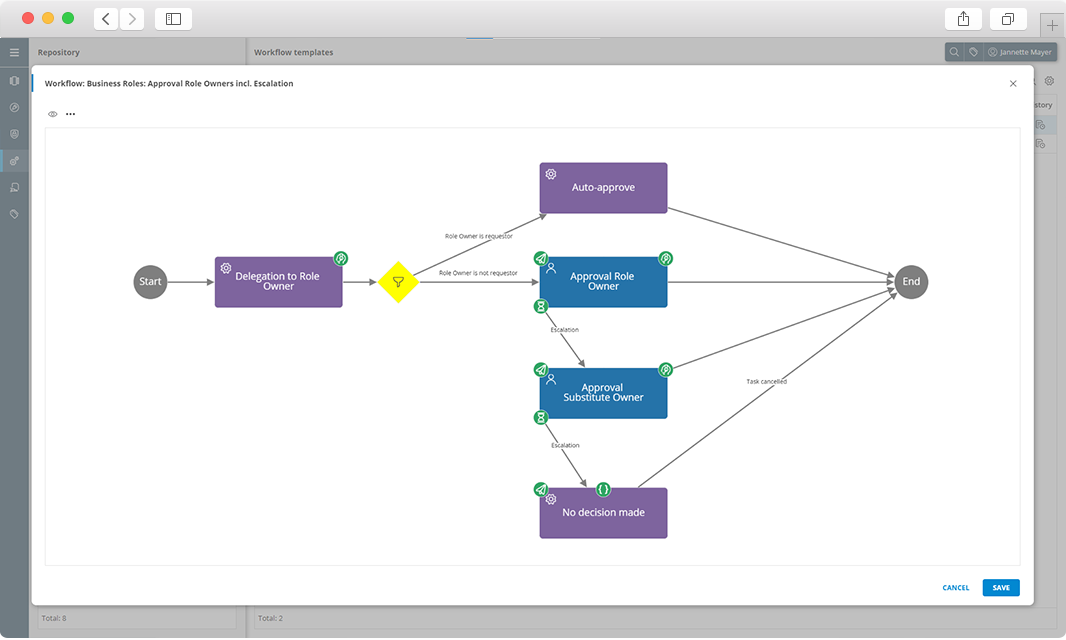
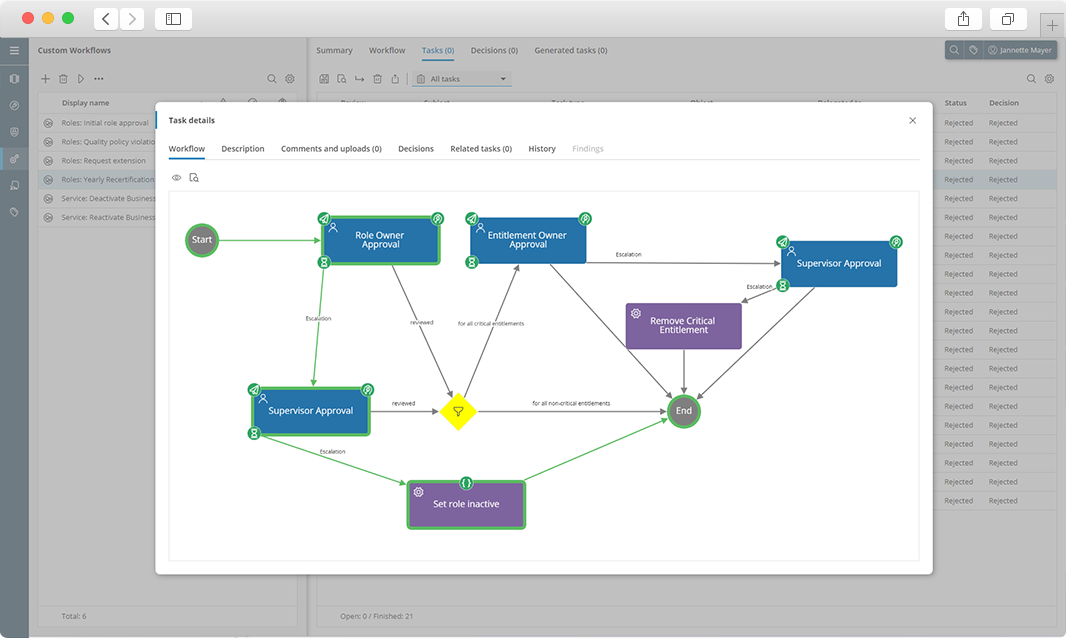
Workflow engine
Regulations and compliance criteria force companies to establish standardized Access Governance processes. Our visual workflow engine allows you to configure and harmonize all required time- and event-based processes, mailings, and escalation procedures with a few clicks.
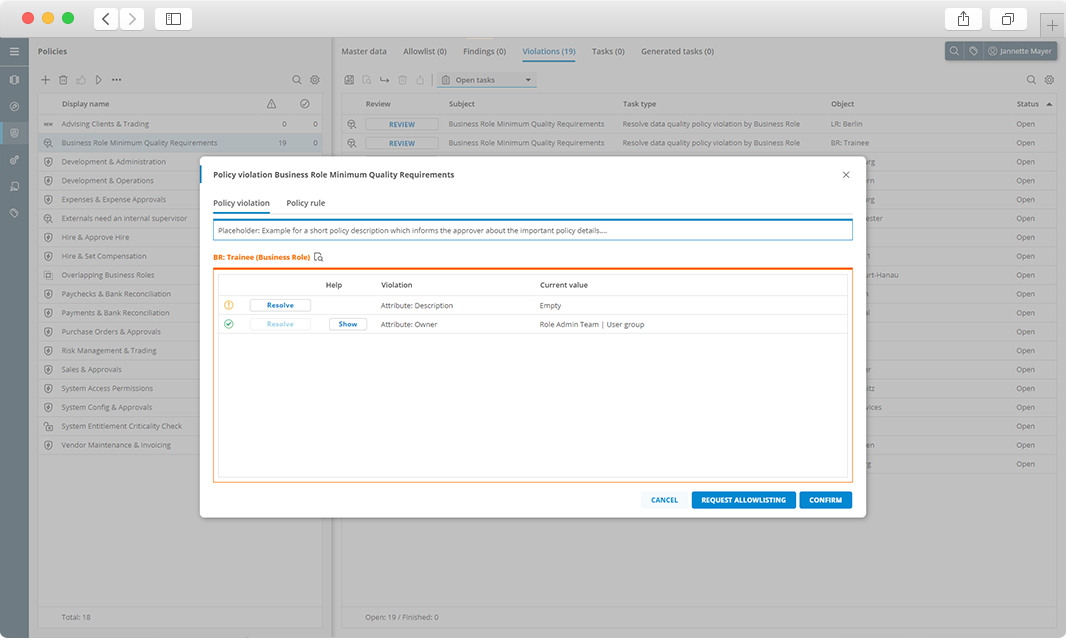
Preventive & detective policy controls
NEXIS 4 ships with a comprehensive policy engine for segregation of duty controls as well as other data quality rule sets. Our intelligent time-based and event-based trigger detect security risks during workflow execution or role modeling. Furthermore, NEXIS 4 can act as real-time policy decision point for any third-party application via our simple API.
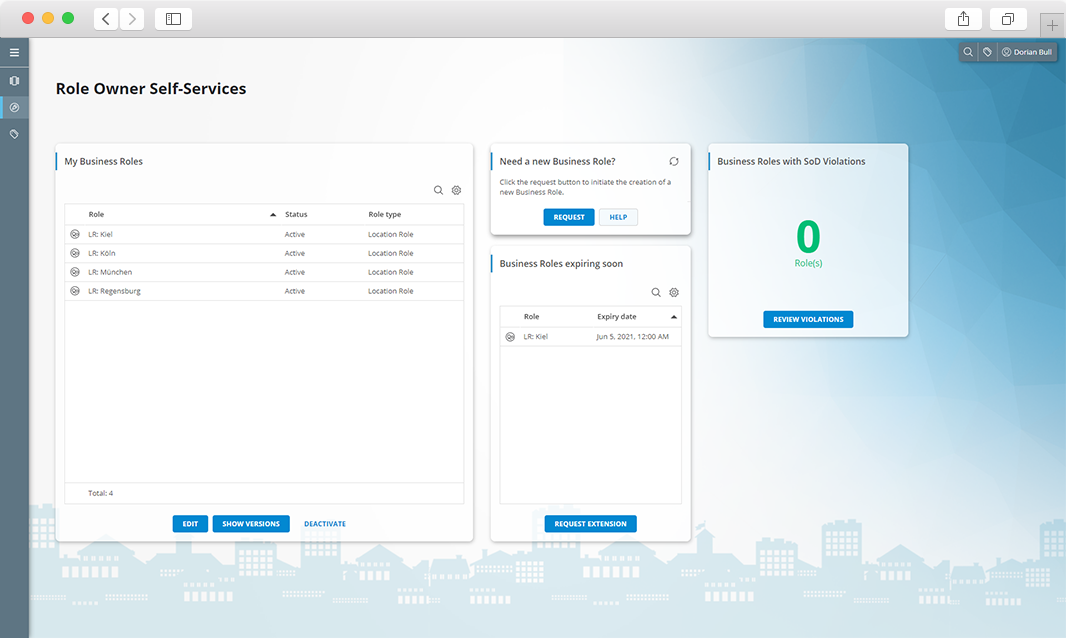
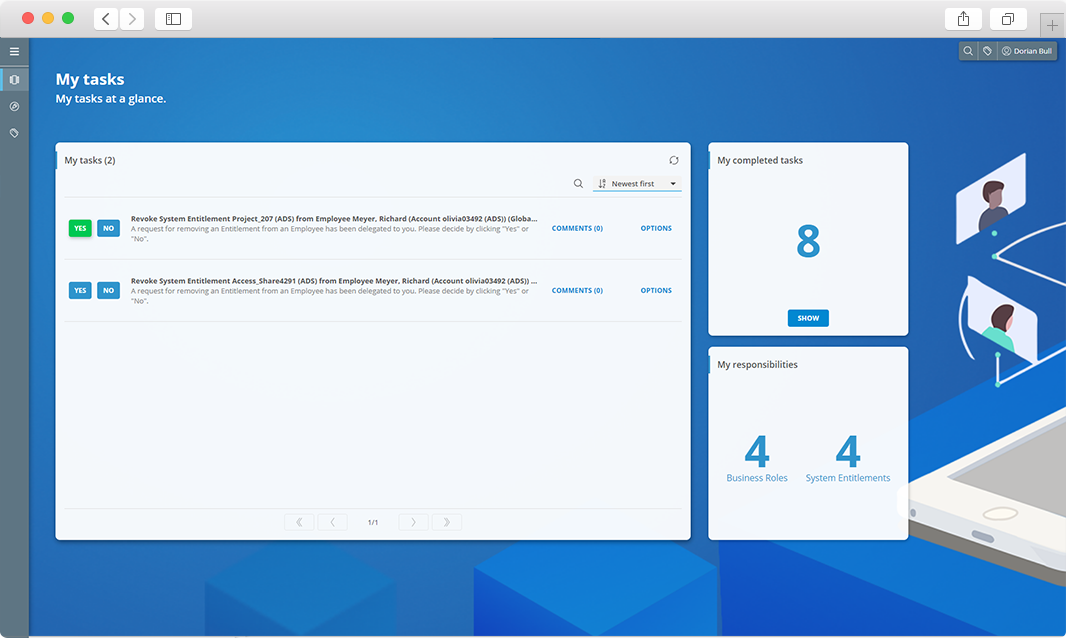
UX-driven self-services
With our service-oriented dashboard approach you are the hero of every end-user: In contrast to complex IAM-solutions, you finally are empowered to provide simple and tailored Access Governance functionalities for everyone. No matter whether you only want to change some colors or re-design the full user interface.
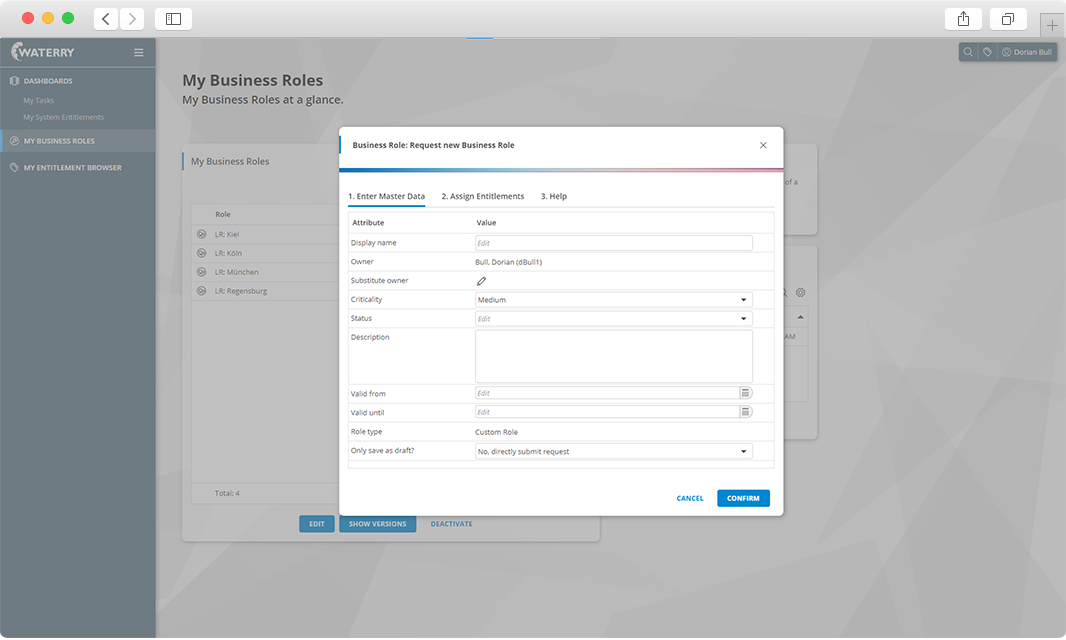
Form management
With our WYSIWYG form editor, your IT staff easily designs, tests, and activates custom forms to cover all your specific business user interaction scenarios.
Dashboards, KPIs & reports
Within minutes you can create your own dashboards and reports according to your needs, generate reports or send them via email. This reduces complexity and maximizes user adoption.
Auditing & reporting
NEXIS 4 provides seamless auditing for all user activities, workflows, and decisions. This way, you can prove at any time, who requested roles, or entitlements, who processed tasks, and who approved which changes.
Frequently asked questions
NEXIS 4 is a standard software for Access Analytics and Governance. We do not directly provision data into your local applications and, in practice, complement existing provisioning engines and IAM-toolings and extend their functionalities.
However, already operating an Identity Management solution is not mandatory for benefitting from NEXIS 4. Our software can be used as stand-alone solution or even as an independent control service for a separately operated IAM-tool.