Identity & Access Analytics
Meet regulatory requirements with demonstrable control over identity risks.Detect toxic access and build a structured inventory across complex landscapes.
Why Identity Transparency is Critical
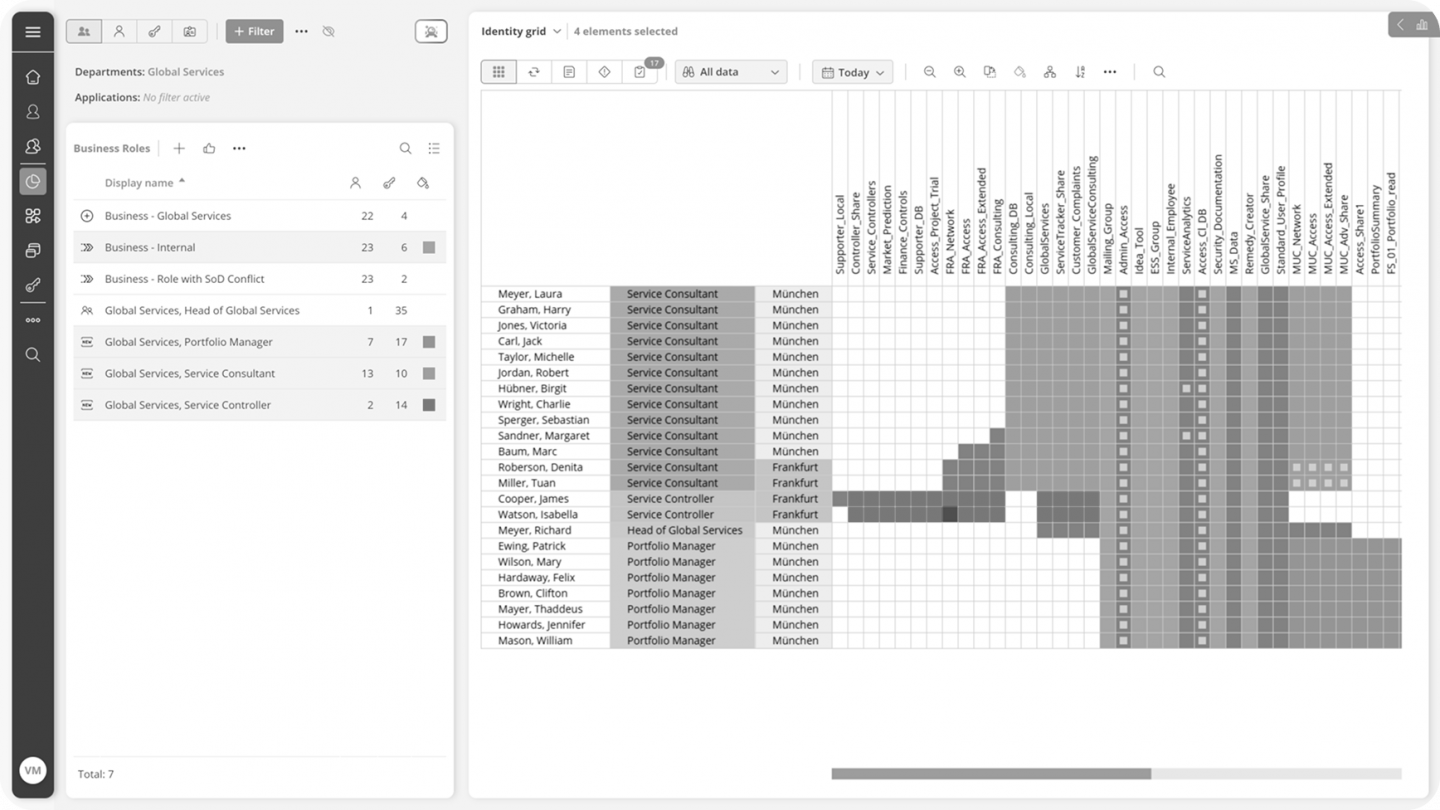
Manual reviews and siloed risk signals make audit preparation reactive. Eliminate visibility gaps across thousands of identities to prevent unnoticed access risks.
Risk Indicators
- Unknown entitlements across legacy systems
- Toxic combinations of roles and permissions
- Orphaned accounts
- Lack of documented access justification
- Fragmented audit evidence
From Identity Transparency to Risk Governance
Identity analytics is not only about visibility.
It is the operational foundation for governance and compliance.
Detected toxic access can automatically:
Feed into Risk Registers
Detected access conflicts and risk indicators can be automatically mapped to enterprise risk registers and control frameworks. Identity risk becomes measurable and formally documented.
Unified Identity Data Model
All connected systems are normalized into a consistent identity structure.
This unified model forms the foundation for continuous governance and cross-domain risk visibility.
Continuous IAM & GRC Alignment
Access risks are linked directly to compliance controls and governance workflows. IAM decisions are no longer isolated technical events but part of enterprise risk management.
Structured Audit Traceability
All detected risks, reviews and remediation actions are documented in a structured, defensible format. Audit preparation shifts from reactive compilation to continuous readiness.
How It Works:
Connect Systems
Integrate IAM, ERP, HR and business applications.
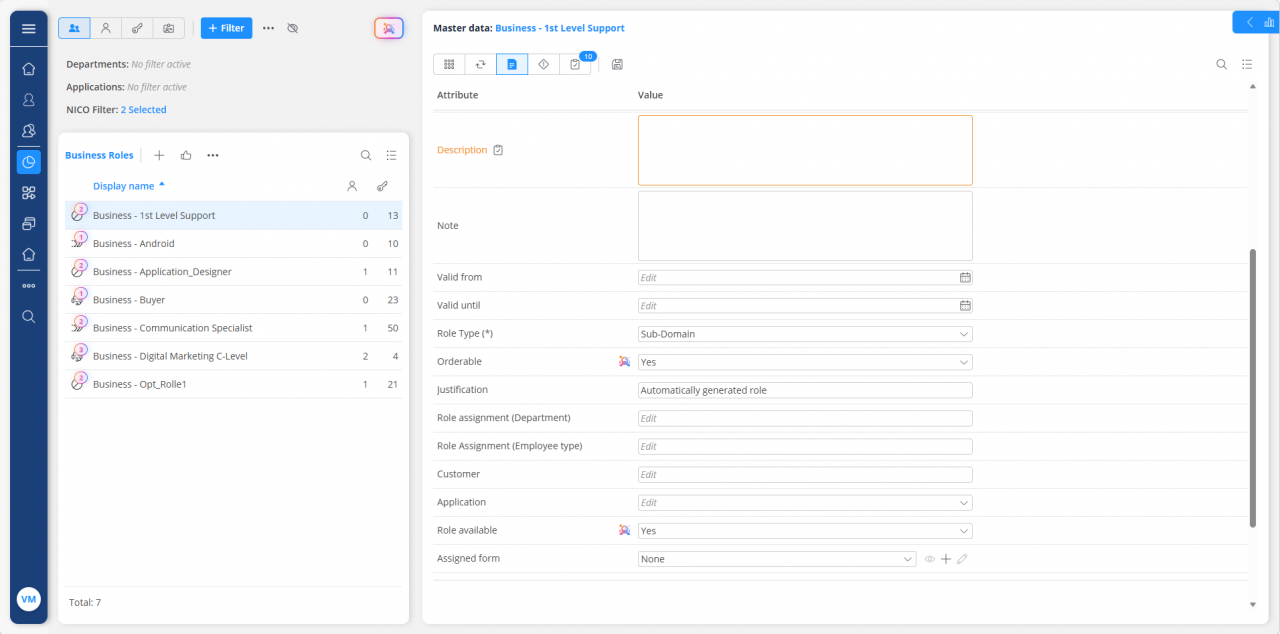
Normalize Identity Data
Standardize identity structures across heterogeneous environments.
Detect & Classify Risks
Apply rule-based and contextual analytics.
Enable Governance Actions
Trigger reviews, remediation workflows and documentation.
How Organizations Apply
Identity & Access Analytics
Audit & Regulatory Compliance
Identity analytics provides:
- A defensible identity inventory
- Structured entitlement transparency
- Automated SoD conflict detection
- Evidence aligned with ISO 27001, DORA and NIS2
Result:
Reduced audit preparation effort and higher evidence quality.
IAM Modernization
Modern IAM initiatives often fail due to unclear role structures and legacy entitlements. Identity analytics supports:
- Role rationalization
- Entitlement cleanup
- Migration readiness
- Transparent baseline assessment
Result:
Faster transformation with reduced risk.
Risk Governance
Access risks are operational risks. Analytics enables:
- Continuous monitoring of toxic access
- Risk classification and prioritization
- Integration into enterprise risk registers
- Escalation workflows
Result:
Identity becomes part of active risk governance, not an isolated IT process.