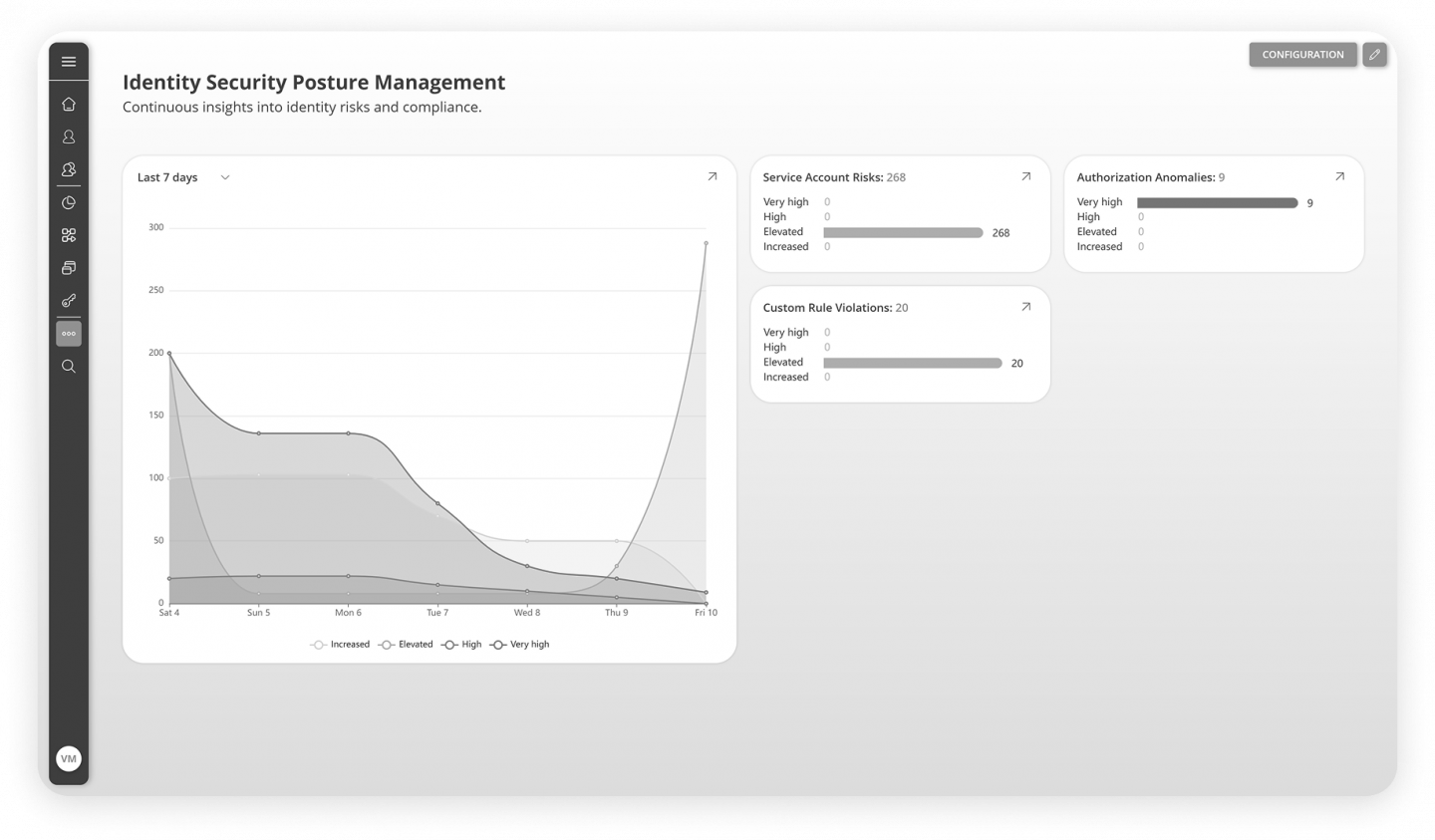
Identity Security Posture Management
Detect identity risks, policy violations, weak access structures, unusual activity, and misassignments before they become incidents. NEXIS extends traditional IAM with continuous monitoring, risk intelligence, and response capabilities across identities, entitlements, and behavior.
Why Identity Security Posture Management Requires Continuous Visibility
Digital identities have become a primary attack surface. Risks such as unusual access patterns, orphaned privileged accounts, redundant entitlements, after-hours assignments, SoD violations across fragmented systems, and misassignments caused by identical names are often invisible to traditional IAM systems until damage is already done. NEXIS ISPM closes that gap with proactive monitoring and automated response.
Risk Indicators
- Anomalies and deviations from historic identity data
- Orphaned or inactive privileged accounts
- Redundant access rights that block revocation workflows
- Entitlements assigned outside working hours
- SoD violations across fragmented systems
- Misassignments caused by identical names
From Identity Data to Continuous Posture Monitoring
NEXIS ISPM continuously ingests and correlates identity-relevant data to detect, evaluate, and resolve vulnerabilities in real time and at admin time. By combining sideloads with NEXIS identity data, it surfaces identity-based threats early and supports faster action before issues escalate. Continuous policy enforcement supports compliance with frameworks such as GDPR, DORA, and NIS2, with audit documentation and versioning built in.
Built On
- Continuous ingestion and correlation of identity data
- Near real-time insights into identity-based threats
- Continuous policy enforcement
- Audit documentation and versioning
- Real-time and admin-time detection and response
Core Capabilities
License Optimization As A Built-In ISPM Capability
License optimization is part of the ISPM capability set. NEXIS analyzes authorization usage, identifies unused roles and permissions, detects inactive or orphaned accounts that still consume licenses, and triggers cleanup workflows to remove unnecessary assignments and reduce waste.
- Usage-Based Authorization Analysis
Focus on what is actively used, not only on what is assigned. - Least-Privilege Cleanup
Identify unused roles and permissions to support least-privilege access. - Inactive Account Detection
Detect inactive or orphaned accounts that still consume licenses. - Automated Cleanup Workflows
Decommission unnecessary authorizations or licenses and reduce waste.
NEXIS License Killer
As a feature pack within NEXIS ISPM, NEXIS License Killer analyzes the actual usage of authorizations, roles, and entitlements rather than assignment alone. Unused access can be identified for remediation, helping reduce attack surface, support least-privilege enforcement, and recover unnecessary license costs.
What The Dashboards Deliver
- Risk KPIs such as high-risk entitlements, SoD conflicts, and orphaned accounts
- Compliance posture aligned with DORA, BAIT, VAIT, and internal policies
- Progress tracking for recertifications, overdue approvals, and escalations
- Remediation backlogs and time-to-fix metrics
- License insights and cost-saving potential

Control Coverage Monitoring
Modern IAM landscapes span IGA, PAM, access management, and business systems. NEXIS ISPM shows which identities, accounts, and entitlements are actively governed and where control gaps remain. It turns governance coverage into measurable KPIs and adds an observability layer across the identity fabric.
- Mapping Of Existing IAM Tools
Map tools to systems and identity populations. - Coverage Visibility
Show which accounts are covered by recertification, SoD checks, and policy enforcement. - Drift Detection
Compare defined authorization concepts with live system states and support automated remediation. - Historical Views
Trace the evolution of controls over time and identify historical blind spots.
How NEXIS ISPM
Creates Operational Impact
Identity Risk & SoD
Identity-related risks often remain hidden across fragmented environments and inconsistent authorization models.
NEXIS ISPM supports:
- Continuous detection of toxic combinations
- Detection of deviations and anomalies
- Monitoring of unusual assignments and access patterns
- Early detection of high-risk identity exposures
Result:
Reduced exposure to hidden access risks and stronger control over SoD violations.
Audit Readiness
Audit preparation becomes difficult when posture data, policy violations, and remediation history are not continuously documented.
NEXIS ISPM supports:
- Continuous evidence of policy enforcement
- Traceable remediation activities
- Visibility into control status and exceptions
- Structured data for audit and review processes
Result:
Higher audit readiness with less manual preparation effort.
Multi Compliance & Scoping
Multiple regulatory frameworks require continuous visibility into control effectiveness and governance coverage.
NEXIS ISPM supports:
- Continuous monitoring of compliance-relevant control gaps
- Identification of uncovered systems and identities
- Support for framework-specific scoping and prioritization
- Structured posture data across multiple compliance contexts
Result:
Identity becomes part of active risk governance, not an isolated IT process.
