Identity Visibility & Intelligence
NEXIS is the Identity Visibility & Intelligence Platform that simplifies IGA and GRC complexity with a connected, explainable view of identity data. From onboarding through roles, authorizations, and audit, it delivers control, compliance, and clarity across identities and access structures.
Why Identity Visibility Matters
Modern IAM environments are distributed across IAM tools, directories, ERP systems, business applications, and cloud platforms. Identity-relevant data is fragmented, relationships are hard to interpret, and governance teams lack a single view of who has access to what, why, and with which risk implications.
Without identity visibility, organizations struggle to improve authorization models, detect governance weaknesses, and establish a reliable foundation for compliance and audit readiness. This is exactly the gap the IVIP category is meant to address: rapid integration and visibility for IAM-relevant data, paired with advanced analytics to improve downstream IAM controls.
Risk Indicators
- No unified view across identity sources and target systems
- Limited transparency into identities, roles, and authorizations
- Weak basis for improving authorization models
- Access risks identified too late
- Audit and compliance efforts depend on manual reconstruction
- IAM controls operate without sufficient context or explainability
From Fragmented IAM Data
to Indentity Intelligence
NEXIS positions IVIP not as another isolated control, but as the intelligence layer that connects IAM-relevant data across varied infrastructures. Dynamic integration consolidates information from multiple sources and turns it into a single, explainable view of identities, relationships, events, and posture. This makes governance more agile and contextually aligned with organizational priorities.
Data consolidation across varied identity infrastructures
Connected view of IAM data, activity, relationships, and posture
Connected view of IAM data, activity, relationships, and posture
Explainable transparency across authorizations and identity structures
Visibility
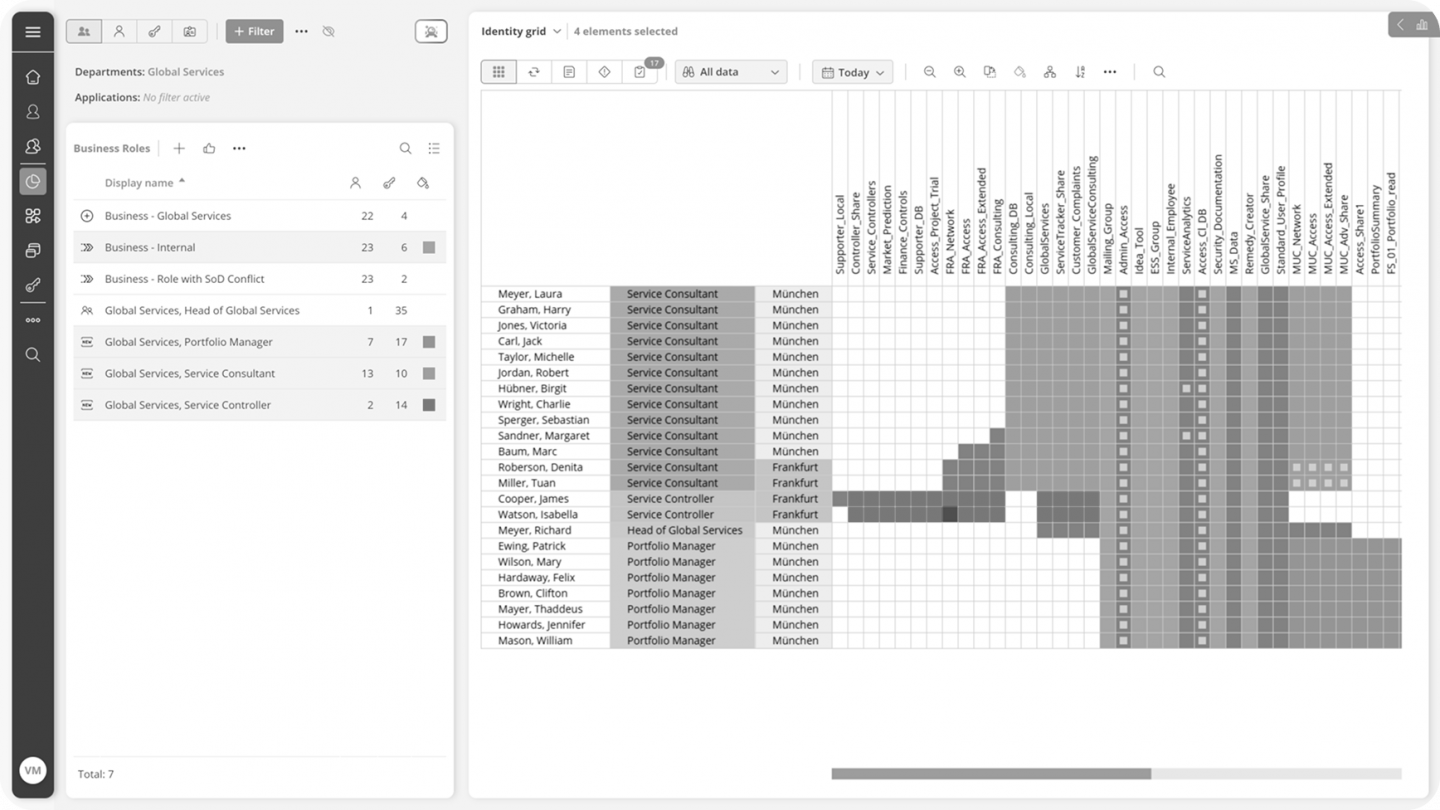
NEXIS IVIP establishes a single, consolidated view of the identity fabric.
It connects to multiple IAM systems and visualizes identities, entitlements and relationships across humans, service accounts, NHIs and AI agents. Complex authorization structures become transparent, including cross-system overlaps and hidden dependencies.
This allows organizations to understand how access actually works – not how it was designed to work.
Intelligence
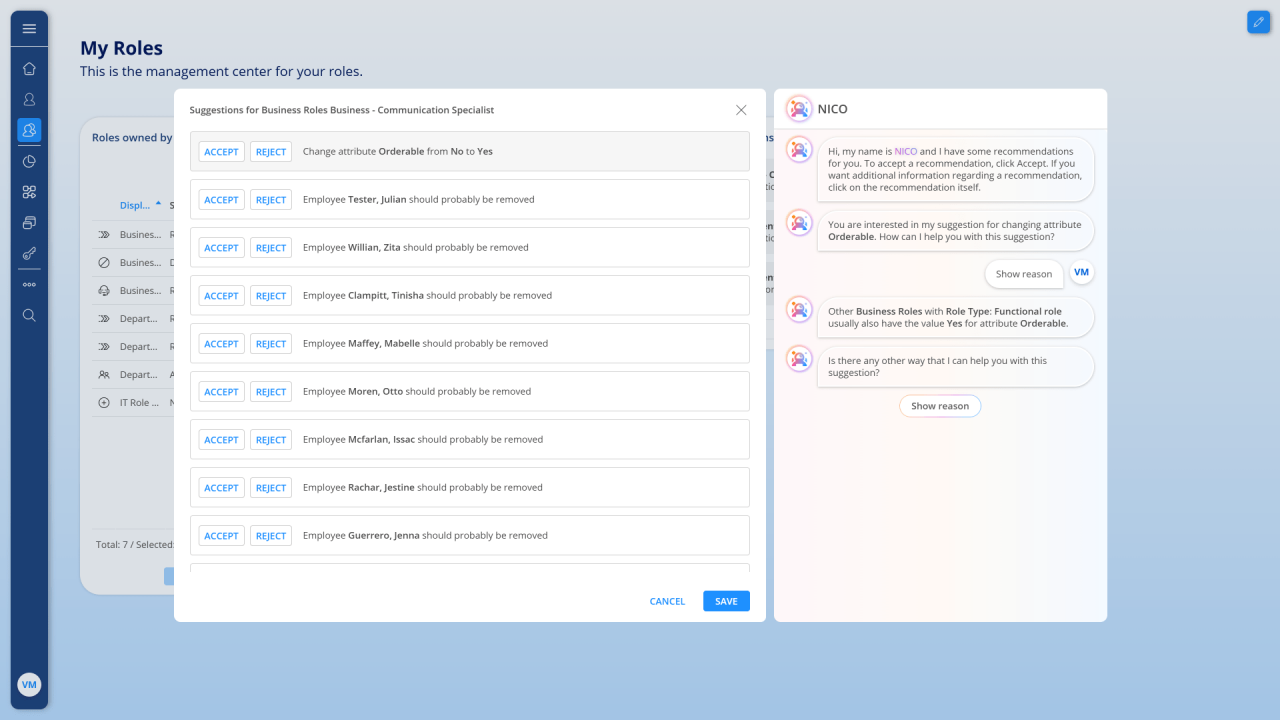
Built-in analytics and AI capabilities turn visibility into understanding.
NEXIS IVIP supports the analysis and continuous improvement of authorization structures by:
- Identifying structural weaknesses in roles and policies
- Detecting excessive, unused or risky access
- Supporting explainable, AI-assisted decisions during governance tasks
Intelligence is transparent, traceable and suitable for regulated environments.
Action
NEXIS IVIP is designed to drive measurable improvement, it enables organizations to act on insights by:
- Improving role models and authorization concepts
- Strengthening Segregation of Duties (SoD) controls across systems
- Reducing access risk for humans, service accounts and AI agents
- Feeding optimized authorization structures back into IGA systems
This establishes a continuous governance loop instead of isolated clean-up initiatives.
How it works
Connect Identity Infrastructures
Connect identity infrastructures
Consolidate and Normalize
Consolidate and normalize
Analyze and Interpret
Use visibility and analytics to understand structures, detect weaknesses, and improve governance quality.
Strengthen Downstream Controls
Use the resulting intelligence to support onboarding, role design, authorization quality, and audit readiness.
Where Identity Visibility & Intelligence Creates Value
Audit & Regulatory Compliance
Regulatory frameworks require complete, current, and auditable evidence of identity governance.
Identity visibility supports:
- Regulatory frameworks require complete, current, and auditable evidence of identity governance.
- Centralized identity inventory
- Continuous SoD monitoring
- Structured audit documentation
Result:
Reduced audit preparation effort and higher evidence quality.
IAM Modernization
Modern IAM initiatives often fail due to unclear role structures and legacy entitlements.
Identity visibility supports:
- Entitlement cleanup
- Migration readiness
- Transparent baseline assessment
Result:
Faster transformation with reduced risk.
