
Continuous Compliance Monitoring with Automated Evidence Collection
Reduce manual audit preparation time while maintaining audit-ready evidence across governed systems, controls, and processes.
Manual Evidence Collection
Delays Audits & Increases Risk
Regulated organizations invest heavily in access controls, yet identity risks continue to emerge. Hybrid environments spanning IGA, PAM, SAP, SaaS, and on-premises systems create visibility gaps that manual controls and isolated rulesets cannot close fast enough.
On one side are toxic combinations: defined entitlement conflicts that can enable fraud or uncontrolled transactions when one person can perform actions that should remain separated. On the other are risks no ruleset fully captures: access accumulation, unused entitlements, role outliers, and anomalies across the authorization landscape.
Both risk types must be governed together. Point solutions that address only one leave structural gaps, and those gaps are often what auditors and attackers find first.
Risk Indicators
- Evidence collection starts weeks before audits
- Application owners collect screenshots manually
- Compliance teams lack current control visibility
- Evidence quality varies across departments
- Gaps are discovered too late
- Documented requirements are not validated against settings
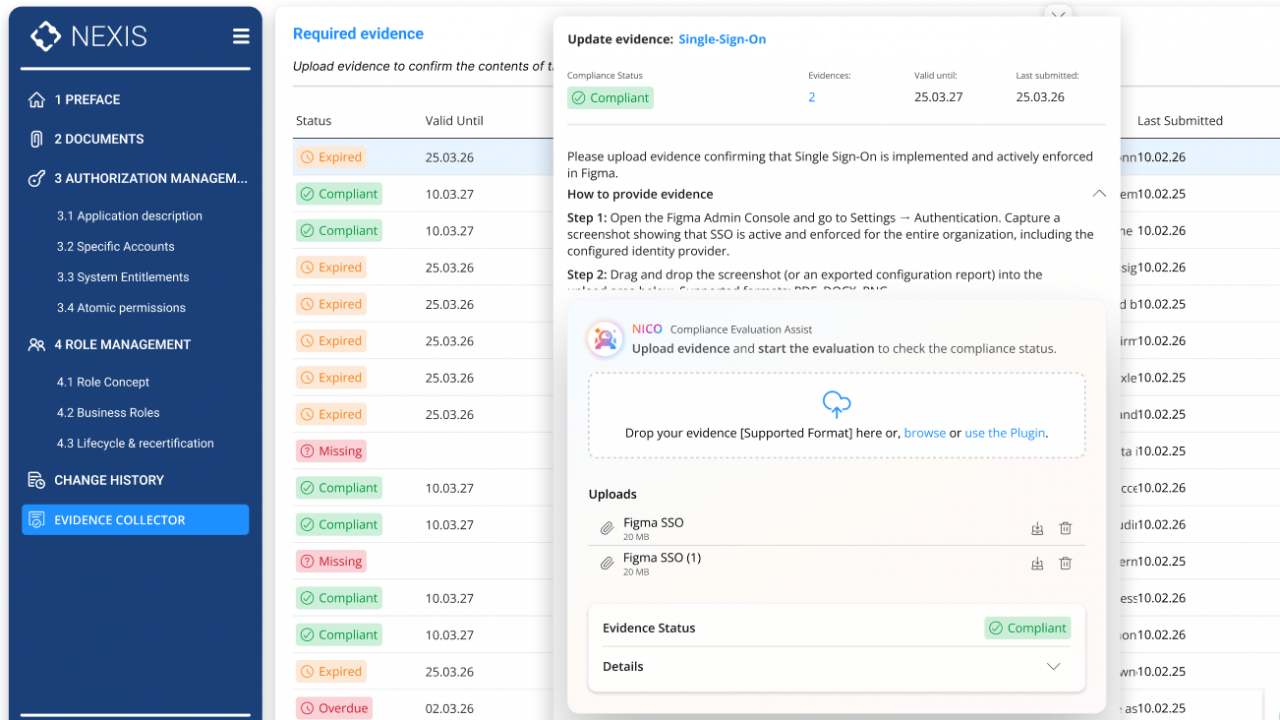
How the NEXIS Evidence Collector Works
NEXIS integrates evidence requirements directly into governance documentation and control frameworks. When a requirement defines what must be proven, the Evidence Collector supports the request, collection, validation, and documentation workflow in one governed process.
Evidence requirements are defined directly within IAM governance documentation or control frameworks. Each requirement can be linked to a specific application, security setting, configuration, or process, with a clear definition of what evidence is acceptable, such as screenshots, configuration exports, log files, or attestations.
System owners, application owners, or responsible departments receive evidence requests through NEXIS workflows. Each request includes context on what must be proven, why it is required, and which format will satisfy the requirement. Requests can be triggered on demand, on schedule, or by events such as application changes or audit cycles.
Responsible parties submit evidence directly in NEXIS through screenshot uploads, configuration files, or textual attestations. Each submission is timestamped, linked to the submitting identity, and retained with version history for comparison across collection periods.
Submitted evidence is evaluated against the defined requirement. This helps identify whether the evidence is complete, whether it shows the required control, or whether it should be flagged for manual review. Compliance teams focus on exceptions rather than manually checking every submission.
Accepted evidence links automatically to the governance documentation or audit framework it supports. Auditors can move directly from a documented requirement to the corresponding evidence, and from the evidence back to the requirement it satisfies.
If submitted evidence reveals a missing control or configuration gap, NEXIS creates remediation tasks for the responsible party. Progress can be tracked, follow-up evidence requested, and the issue closed with a documented audit trail before the next audit cycle begins.
Evidence Collection Becomes
Continuous, Not Crisis-Driven
With NEXIS Evidence Collector, audit preparation shifts from weeks of manual coordination to a faster process centered on retrieving evidence that is already available. Compliance teams gain clearer visibility into current control effectiveness, while system owners incorporate evidence collection into normal operations instead of treating it as a separate audit task.
The result:
Audit-ready documentation on demand
AI-assisted evidence validation
Continuous visibility into control effectiveness
Foundation for broader CCM automation
Evidence Collector in Practice
Application Security Configuration Compliance
IAM governance documentation requires specific security settings enabled in integrated applications - password complexity, session timeout, encryption standards. Manual verification is periodic and reactive.
What NEXIS provides
- Evidence requirements defined in IAM governance documentation
- Automated requests sent to application owners quarterly or on-demand
- Screenshot-based evidence collection with AI validation of visible settings
- Automatic documentation linkage for auditor access
Result:
Application security compliance becomes continuously verifiable instead of an audit-preparation exercise.
Segregation of Duties (SoD) Enforcement Proof
When SoD policies identify high-risk conflicts or require compensating controls, NEXIS can support evidence collection.
What NEXIS provides:
- Evidence requests automatically generated from SoD policy violations or high-risk combinations
- Risk owners submit evidence of compensating controls or remediation
- AI validation confirms evidence addresses identified SoD risk
- Complete audit trail from SoD policy to violation detection to evidence and resolution
Result:
SoD compliance becomes demonstrable with timestamped evidence trail rather than relying on point-in-time reports.
IAM Governance Documentation Validation
When governance documentation defines role models, approval workflows, or lifecycle processes, NEXIS can embed the related evidence requirement directly into the documentation.
What NEXIS provides:
- Evidence requirements embedded in governance documentation
- Workflow-based evidence collection from process participants
- AI validation that collected evidence matches documented procedures
- Version-controlled evidence showing process consistency over time
Result:
Governance documentation becomes evidence-backed and operational, rather than a static reference questioned during audits.
