Third-Party Risk Management That Holds Up Under Scrutiny
NEXIS centralizes supplier and ICT provider oversight, from risk classification and automated self-assessments to audit-ready documentation. One platform supports DORA, NIS2, and internal governance requirements.
Why Third-Party Risk Becomes a Governance Problem
DORA Articles 28-30 and NIS2 have turned third-party risk into a compliance obligation. Regulators expect structured oversight of ICT providers, supplier dependencies, and outsourcing risk.
In many organizations, providers are still onboarded without structured risk assessment. Self-assessments run through email and spreadsheets, provider registers are incomplete, and evidence must be compiled manually when audits begin.
The result is avoidable exposure. Critical providers may not be linked to business processes, incidents cannot be traced clearly, and oversight gaps only become visible when proof is requested.
Risk Indicators
- No centralized provider and contract register
- Self-assessments run through email and spreadsheets
- Sub-contractor relationships are not visible
- Risk classifications are disconnected from business processes
- Audit evidence is assembled ad hoc
- Incidents cannot be traced to providers
How NEXIS Structures Third-Party Oversight
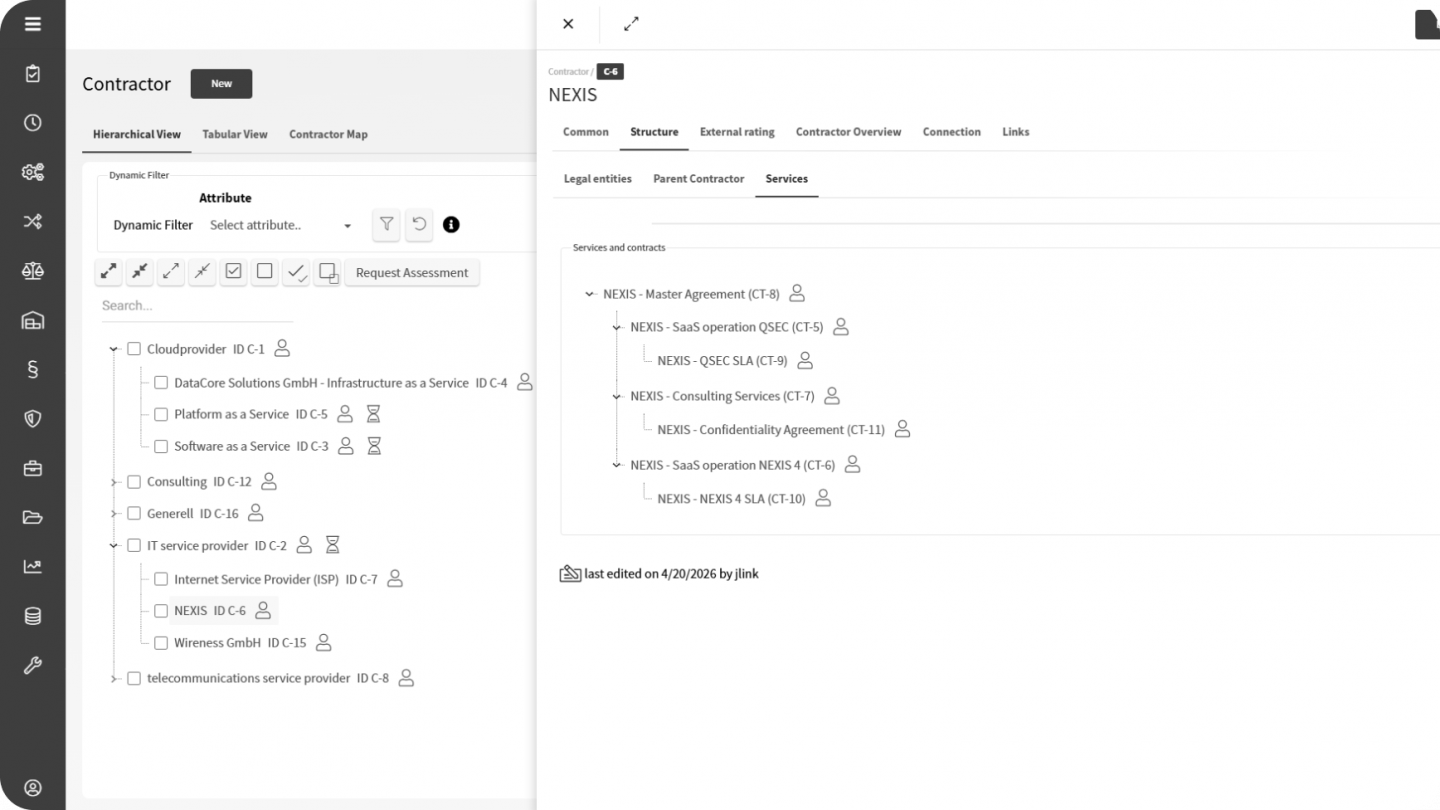
- Register Providers
Build and maintain a current provider register with contracts, relationships, ownership, and risk-relevant attributes. - Assess and Classify
Run structured self-assessments and evaluate providers across defined risk categories. - Connect to Operations
Link provider risks to business processes, assets, incidents, and continuity assessments. - Monitor and Report
Track status, thresholds, and reassessment cycles while generating audit-ready reports and evidence on demand.
Applied to the Situations That Compliance Teams Actually Face
ICT Third-Party Risk Under DORA
Financial institutions must maintain a current register of ICT third-party providers, assess their risk, and demonstrate ongoing oversight. Under DORA, this includes contractual obligations, monitoring, and exit-related readiness.
NEXIS supports:
- Centralized provider register with contractual and risk data
- Periodic and event-driven assessment cycles
- Documented monitoring activities for regulatory review
- Integration with ICT risk controls and internal control frameworks
Result:
DORA-related third-party governance becomes demonstrable, with evidence available on demand.
Supply Chain Compliance Under NIS2 and LkSG
NIS2 and the German Supply Chain Act require structured oversight of supplier risks and due diligence across the supply chain. Point-in-time assessments are not enough when providers, dependencies, and obligations change continuously.
NEXIS supports:
- Mapping of sub-contractors and hierarchical provider structures
- Configurable risk categories for security and regulatory criteria
- Direct provider engagement through the Third Party portal
- Full audit trail for assessments and follow-up actions
Result:
Supply chain oversight remains continuous, traceable, and aligned to both NIS2 and LkSG requirements.
Outsourcing Management in Banking and Insurance
BAIT and VAIT require banks and insurers to apply structured risk management to outsourced functions. Provider criticality, reassessment cycles, and evidence of monitoring must remain current and defensible.
NEXIS supports:
- Risk classification by outsourcing type and provider criticality
- Integration with BIA and business process continuity
- Automated reassessment scheduling and escalation workflows
- Reporting aligned to BAIT and VAIT evidence requirements
Result:
Outsourcing registers and risk assessments stay current instead of being rebuilt at audit time.
Third-Party Risk and External AI Services
External AI Services Are a New Third-Party Risk Category
As organizations adopt AI services hosted outside their own environment, a new class of third-party risk emerges. These services access corporate data, influence decisions, and operate within business processes, yet they often sit outside traditional provider governance.
NEXIS extends third-party governance to this category by allowing external AI agents and services to be registered, classified, assessed, and linked to the identity governance processes that control the non-human identities or agents interacting with them. This brings provider governance and identity governance together in one platform, rather than treating them as separate control problems.
Built for the Frameworks That Require Third-Party Oversight
NEXIS supports third-party governance across the regulatory frameworks that require structured oversight of suppliers, ICT providers, and outsourcing relationships.
