Structured Risk Management Across Cyber, Enterprise, and Third Parties
NEXIS delivers a structured, audit-ready approach to enterprise and cyber risk management, covering risk registers, third-party dependencies, and regulatory alignment with DORA, NIS2, and ISO 27001 in one platform.
Risk Is No Longer an IT Problem. It Is a Business Imperative.
Cyberattacks are more targeted, supply chains are more exposed, and regulators increasingly require continuous, documented risk processes. DORA, NIS2, and ISO 27001 no longer support periodic review alone.
Many organizations still manage enterprise and IT risks, third-party risks, and related evidence in separate tools or manual processes. This creates blind spots, slows reporting, and weakens traceability.
Structured enterprise cyber risk management connects enterprise and cyber risk, operational resilience, and identity-related exposure in one governed model across the organization.
Risk Indicators
- No single view across enterprise, IT and supplier risks
- Risk assessments happen manually or too late
- DORA and NIS2 documentation does not scale
- Supplier risks are assessed irregularly
- Evidence for regulators is slow to retrieve
- Access and cyber risks are managed separately
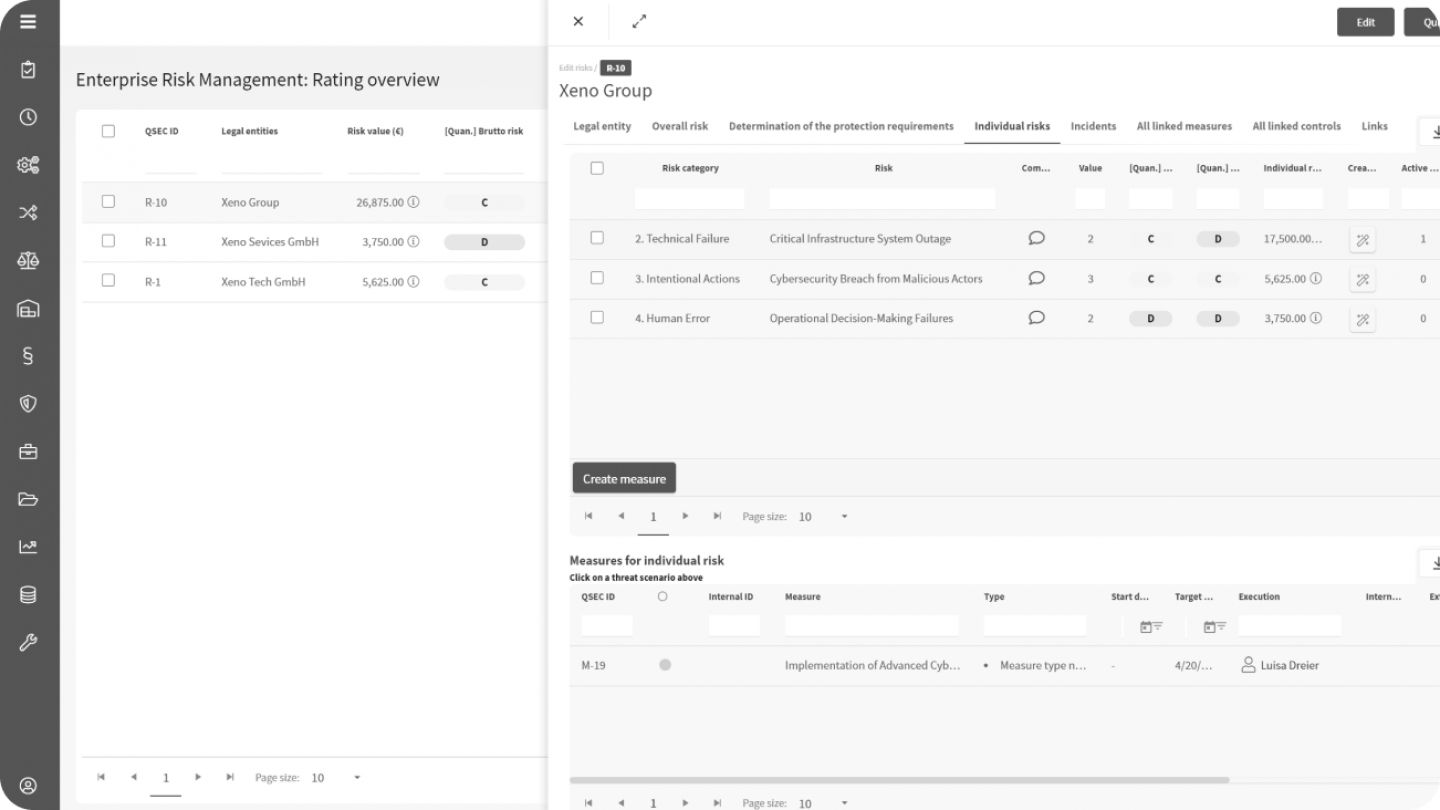
How NEXIS Manages Enterprise and Cyber Risks
NEXIS brings IT, cyber, and third-party risks together in one structured register instead of leaving them scattered across tools, spreadsheets, and point solutions. Risk posture becomes continuously maintained, easier to evaluate, and ready to report when regulators, auditors, or management request evidence.
- Identify and Assess
Map IT, cyber, and third-party risks into one structured register with consistent categories and ownership and relate them to enterprise risks. - Evaluate and Quantify
Prioritize treatment using qualitative and quantitative methods based on likelihood, impact, and regulatory relevance. - Treat and Control
Define treatment measures, assign responsibility, and connect access controls where identity risk intersects with cyber risk. - Monitor and Report
Use dashboards and on-demand reporting to provide structured evidence for regulators, management, and internal auditors.
NEXIS Platform Capabilities
For Risk-Aware Governance
Pre-Configured for Every Relevant Risk Framework
NEXIS supports third-party governance across the regulatory frameworks that require structured oversight of suppliers, ICT providers, and outsourcing relationships.
Recognized for Combining GRC and Enterprise Identity Intelligence
NEXIS is positioned around a governance model in which GRC risk management and identity intelligence share a common data foundation. This closes the gap between what risk exists, who has access, and how both must be governed in real time.
This combination is especially relevant where risk posture, compliance evidence, and identity-related exposure must be assessed together rather than across disconnected tools.
