
Role Mining for IAM
Turn Unstructured Access Into Governed, Audit-Ready Role Models
Without a Structured Role Model, Identity Governance Has No Foundation
Most organizations accumulate entitlements over time without a structured role model. Access is assigned ad hoc, inherited, or copied from outdated templates.
The result is limited transparency into who has what access, why it was granted, and whether it still applies. Recertifications become difficult to defend, audits require manual effort, and IGA programs are built on access data that is hard to trust. Role mining for IAM creates structure from that reality. It establishes a governed foundation for role design, validation, and continuous improvement.
Risk Indicators
- Access is assigned individually with no reusable role structure
- Entitlement inventories have grown without clear grouping logic
- Business teams cannot validate technical access objects
- SoD conflicts are discovered late in audit or review cycles
- Provisioning depends on spreadsheets, scripts, or manual workarounds
- Role ownership is unclear across systems and departments
A Role Model Ready for Governance
Before role mining, access is often assigned ad hoc, reviewed manually, and difficult to explain. With NEXIS, role models become structured, reviewable, business-owned, and ready to support governed access provisioning.
Roles Aligned to Real Job Functions or Policies
Owned by Business Stakeholders
Compliant from Creation
Ready to Feed Directly into IGA Provisioning
With NEXIS, a Role Model is the Starting Point – Not the End Goal
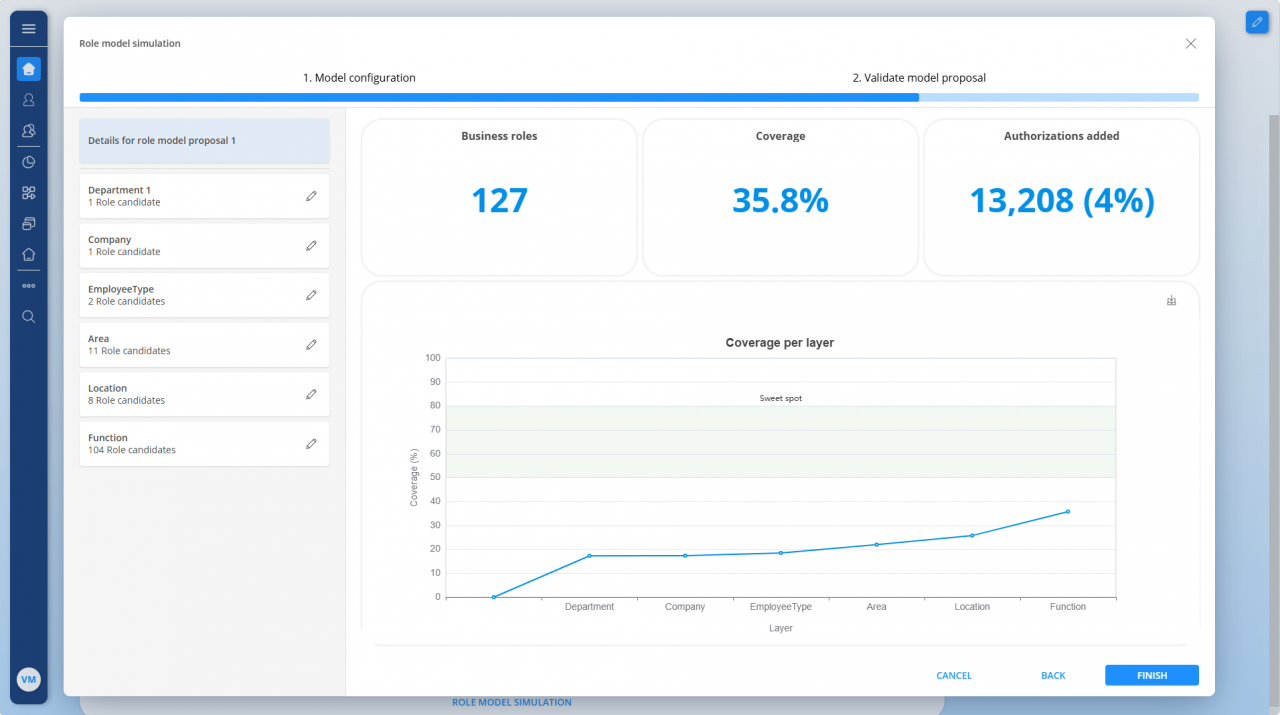
NEXIS Role Mining gives organizations a structured path from unmanaged entitlement data to a governed role model that business teams can understand and own. For IAM programs at an early stage, it creates the foundation for scalable governance. For mature environments, it helps identify what should be cleaned up, optimized, or retired.
Role candidates aligned to job functions and organizational structure
SoD rules embedded from the start of role design
Business owners able to review and approve without technical IAM expertise
Results that feed directly into existing IGA provisioning environments
Related NEXIS Platform Capabilities
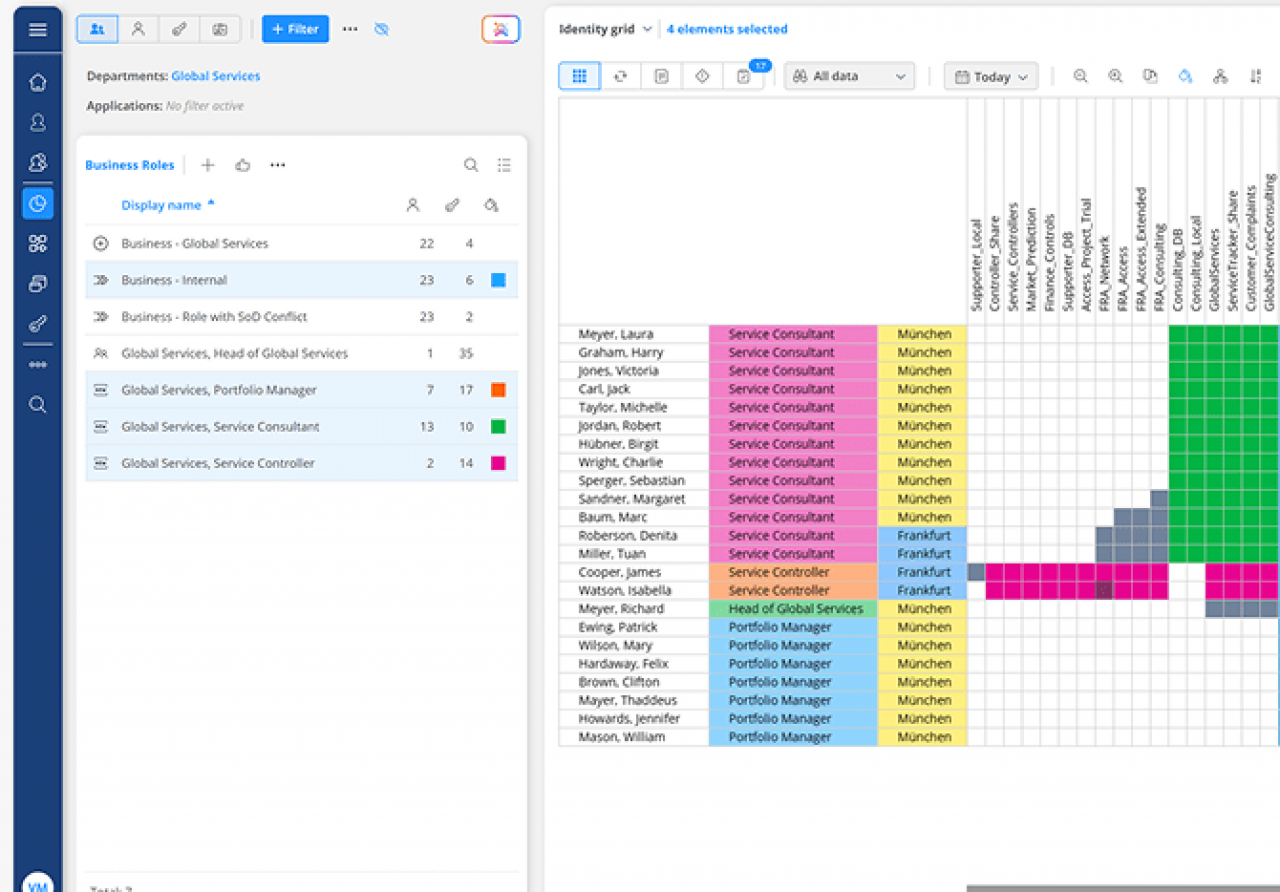
Analyze entitlement data, identify access patterns, and detect role candidates, outliers, and cleanup needs.
Create business-aligned role models with clear ownership, lifecycle control, and stronger governance over time.
Embed SoD controls into role design to detect conflicting access early and strengthen governance before publication.
Support role mining with structured documentation, defined ownership, and audit-ready governance records.
