Role & Access Governance
NEXIS brings role design, access governance, recertification, and Segregation of Duties controls into one continuous process. It replaces fragmented reviews, static role models, and manual approval chains with analytics, governance workflows, and integrated control mechanisms that work across IGA, PAM, SaaS, and legacy environments.
Why Role and Access Governance Needs a New Approach
Hybrid IT, SaaS sprawl, and growing regulatory requirements make static role models and campaign-based access control harder to sustain. Manual recertifications, e-mail approvals, and spreadsheet-driven role maintenance do not scale and make audit-ready governance difficult. NEXIS addresses this with a continuous model that combines role analytics, approval workflows, recertifications, and SoD validation.
Risk Indicators
- Fragmented and outdated role models
- Toxic combinations of roles and permissions
- Manual review and approval effort
- SoD conflicts detected too late
- Low traceability across changes and approvals
- Audit pressure caused by weak governance processes
From Static Role Models to Continuous Governance
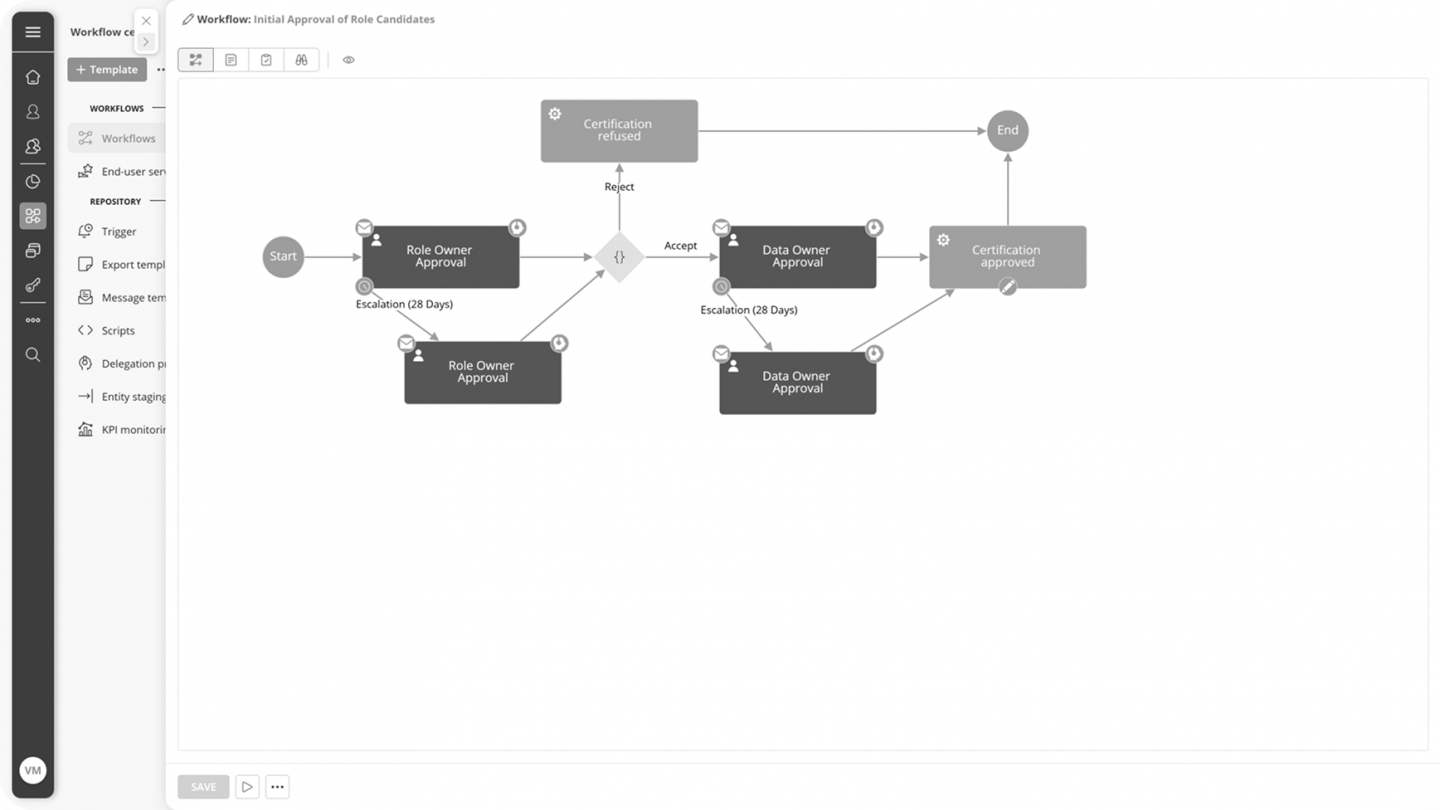
NEXIS turns role and access governance into a continuous process. Role mining, analytics, workflow automation, recertification, and SoD controls work together to keep access structures effective over time. This supports everything from role discovery and cleanup to approval routing, exception handling, and ongoing optimization.
Built On
- Role discovery based on analytics, clustering, and pattern recognition
- Time- and event-triggered recertifications
- Centrally managed governance documentation with version history
Core Capabilities
How Role & Access Governance
Creates Operational Impact
IAM Modernization
Legacy role models and fragmented entitlement structures often slow down IAM transformation.
Role and access governance supports:
- Role rationalization
- Entitlement cleanup
- Governance-ready target models
- Controlled migration preparation
Result:
Cleaner role structures and faster modernization with reduced governance risk.
Access Reviews
Cleaner role structures and faster modernization with reduced governance risk.
Role and access governance supports:
- Structured review campaigns
- Clear ownership and accountability
- Repeatable approval workflows
- Traceable review decisions
Result:
More efficient reviews, better completion rates, and stronger auditability.
Identity Risk & SoD
Conflicting access rights and weak role structures increase operational and compliance risk.
Role and access governance supports:
- Role-based SoD validation
- Detection of toxic combinations
- Risk-aware access decisions
- Continuous governance controls
Result:
Identity becomes part of active risk governance, not an isolated IT process.
